- Автоматизация
- Антропология
- Археология
- Архитектура
- Биология
- Ботаника
- Бухгалтерия
- Военная наука
- Генетика
- География
- Геология
- Демография
- Деревообработка
- Журналистика
- Зоология
- Изобретательство
- Информатика
- Искусство
- История
- Кинематография
- Компьютеризация
- Косметика
- Кулинария
- Культура
- Лексикология
- Лингвистика
- Литература
- Логика
- Маркетинг
- Математика
- Материаловедение
- Медицина
- Менеджмент
- Металлургия
- Метрология
- Механика
- Музыка
- Науковедение
- Образование
- Охрана Труда
- Педагогика
- Полиграфия
- Политология
- Право
- Предпринимательство
- Приборостроение
- Программирование
- Производство
- Промышленность
- Психология
- Радиосвязь
- Религия
- Риторика
- Социология
- Спорт
- Стандартизация
- Статистика
- Строительство
- Технологии
- Торговля
- Транспорт
- Фармакология
- Физика
- Физиология
- Философия
- Финансы
- Химия
- Хозяйство
- Черчение
- Экология
- Экономика
- Электроника
- Электротехника
- Энергетика
ИТОГО – ЕВА – АВЕ = СВЯТАЯ + НГЕЛИОН - ЛИГНОН = КОЛЫБЕЛЬ 1 страница
| ||||||||||||||||||||||||||||||||||||||||
| Baconian Cipher a AAAAA g AABBA m ABABB s BAAAB y BABBA b AAAAB h AABBB n ABBAA t BAABA z BABBB c AAABA i ABAAA o ABBAB u BAABB d AAABB j BBBAA p ABBBA v BBBAB e AABAA k ABAAB q ABBBB w BABAA f AABAB l ABABA r BAAAA x BABAB
|
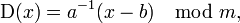
Affine Cipher In the affine cipher the letters of an alphabet of size m are first mapped to the integers in the range 0..m - 1. It then uses modular arithmetic to transform the integer that each plaintext letter corresponds to into another integer that correspond to a ciphertext letter. The encryption function for a single letter is 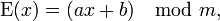 where modulus m is the size of the alphabet and a and b are the key of the cipher. The value a must be chosen such that a and m are coprime. Considering the specific case of encrypting messages in English (i.e. m = 26), there are a total of 286 non-trivial affine ciphers, not counting the 26 trivial Caesar ciphers. This number comes from the fact there are 12 numbers that are coprime with 26 that are less than 26 (these are the possible values of a). Each value of a can have 26 different addition shifts (the b value) ; therefore, there are 12*26 or 312 possible keys. Plaintext: lignone where modulus m is the size of the alphabet and a and b are the key of the cipher. The value a must be chosen such that a and m are coprime. Considering the specific case of encrypting messages in English (i.e. m = 26), there are a total of 286 non-trivial affine ciphers, not counting the 26 trivial Caesar ciphers. This number comes from the fact there are 12 numbers that are coprime with 26 that are less than 26 (these are the possible values of a). Each value of a can have 26 different addition shifts (the b value) ; therefore, there are 12*26 or 312 possible keys. Plaintext: lignone
mjhopof iztoron epfotov afrovod wvdoxol slpozot krnodoj ghzofor cxlohoz ynxojoh udjolop qtvonox nkipqpg jaupspo fqgpupw bgspwpe xwepypm tmqpapu lsopepk hiapgps dympipa zoypkpi vekpmpq ruwpopy oljqrqh kbvqtqp grhqvqx chtqxqf yxfqzqn unrqbqv mtpqfql ijbqhqt eznqjqb apzqlqj wflqnqr svxqpqz pmkrsri lcwrurq hsirwry diuryrg zygraro vosrcrw nuqrgrm jkcriru faorkrc bqarmrk xgmrors twyrqra qnlstsj mdxsvsr itjsxsz ejvszsh azhsbsp wptsdsx ovrshsn kldsjsv gbpslsd crbsnsl yhnspst uxzsrsb romtutk neytwts juktyta fkwtati baitctq xqutety pwstito lmetktw hcqtmte dsctotm ziotqtu vyatstc spnuvul ofzuxut kvluzub glxubuj cbjudur yrvufuz qxtujup mnfulux idrunuf etdupun ajpuruv wzbutud tqovwvm pgavyvu lwmvavc hmyvcvk dckvevs zswvgva ryuvkvq nogvmvy jesvovg fuevqvo bkqvsvw xacvuve urpwxwn qhbwzwv mxnwbwd inzwdwl edlwfwt atxwhwb szvwlwr ophwnwz kftwpwh gvfwrwp clrwtwx ybdwvwf vsqxyxo ricxaxw nyoxcxe joaxexm femxgxu buyxixc tawxmxs pqixoxa lguxqxi hwgxsxq dmsxuxy zcexwxg wtryzyp sjdybyx ozpydyf kpbyfyn gfnyhyv cvzyjyd ubxynyt qrjypyb mhvyryj ixhytyr entyvyz adfyxyh xuszazq tkezczy paqzezg lqczgzo hgozizw dwazkze vcyzozu rskzqzc niwzszk jyizuzs fouzwza begzyzi yvtabar ulfadaz qbrafah mrdahap ihpajax exbalaf wdzapav stlarad ojxatal kzjavat gpvaxab cfhazaj zwubcbs vmgbeba rcsbgbi nsebibq jiqbkby fycbmbg xeabqbw tumbsbe pkybubm lakbwbu hqwbybc dgibabk axvcdct wnhcfcb sdtchcj otfcjcr kjrclcz gzdcnch yfbcrcx uvnctcf qlzcvcn mblcxcv irxczcd ehjcbcl bywdedu xoidgdc teudidk pugdkds lksdmda haedodi zgcdsdy vwodudg rmadwdo ncmdydw jsydade fikdcdm czxefev ypjehed ufvejel qvhelet mlteneb ibfepej ahdetez wxpeveh snbexep odnezex ktzebef gjleden dayfgfw zqkfife vgwfkfm rwifmfu nmufofc jcgfqfk biefufa xyqfwfi tocfyfq peofafy luafcfg hkmfefo ebzghgx arlgjgf whxglgn sxjgngv onvgpgd kdhgrgl cjfgvgb yzrgxgj updgzgr qfpgbgz mvbgdgh ilngfgp fcahihy bsmhkhg xiyhmho tykhohw powhqhe leihshm dkghwhc zashyhk vqehahs rgqhcha nwchehi jmohghq gdbijiz ctnilih yjzinip uzlipix qpxirif mfjitin elhixid abtizil wrfibit shridib oxdifij knpihir hecjkja duojmji zkajojq vamjqjy rqyjsjg ngkjujo fmijyje bcujajm xsgjcju tisjejc pyejgjk loqjijs ifdklkb evpknkj albkpkr wbnkrkz srzktkh ohlkvkp gnjkzkf cdvkbkn ythkdkv ujtkfkd qzfkhkl mprkjkt jgelmlc fwqlolk bmclqls xcolsla tsaluli pimlwlq hoklalg dewlclo zuilelw vkulgle raglilm nqslklu khfmnmd gxrmpml cndmrmt ydpmtmb utbmvmj qjnmxmr iplmbmh efxmdmp avjmfmx wlvmhmf sbhmjmn ortmlmv lignone hysnqnm doensnu zeqnunc vucnwnk rkonyns jqmncni fgynenq bwkngny xmwning tcinkno psunmnw
|
| ROT13 Cipher
|
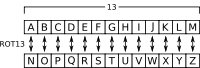
Polybius Square  A Polybius Square is a table that allows someone to translate letters into numbers. To give a small level of encryption, this table can be randomized and shared with the recipient. In order to fit the 26 letters of the alphabet into the 25 spots created by the table, the letters i and j are usually combined. A Polybius Square is a table that allows someone to translate letters into numbers. To give a small level of encryption, this table can be randomized and shared with the recipient. In order to fit the 26 letters of the alphabet into the 25 spots created by the table, the letters i and j are usually combined.
l i g n o n e 1 4 2 3 4 3 5 3 2 2 3 3 3 1 They are then read out in rows:
| ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Permutation Cipher In classical cryptography, a permutation cipher is a transposition cipher in which the key is a permutation. To apply a cipher, a random permutation of size E is generated (the larger the value of E the more secure the cipher). The plaintext is then broken into segments of size E and the letters within that segment are permuted according to this key. In theory, any transposition cipher can be viewed as a permutation cipher where E is equal to the length of the plaintext; this is too cumbersome a generalisation to use in actual practice, however. The idea behind a permutation cipher is to keep the plaintext characters unchanged, butalter their positions by rearrangement using a permutation This cipher is defined as: Let m be a positive integer, and K consist of all permutations of {1,...,m} For a key (permutation)  , define: The encryption function , define: The encryption function 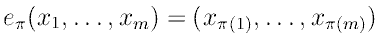 The decryption function The decryption function 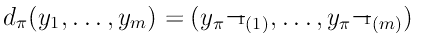 A small example, assuming m = 6, and the key is the permutation A small example, assuming m = 6, and the key is the permutation  : : 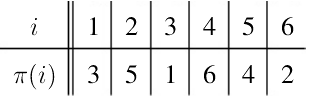 The first row is the value of i, and the second row is the corresponding value of The first row is the value of i, and the second row is the corresponding value of  (i) The inverse permutation, (i) The inverse permutation,  is constructed by interchanging the two rows, andrearranging the columns so that the first row is in increasing order, Therefore, is constructed by interchanging the two rows, andrearranging the columns so that the first row is in increasing order, Therefore,  is: is: 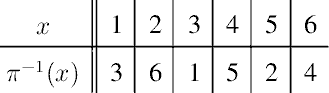 Total variation formula: Total variation formula:  e = 2,718281828 , n - plaintext length Plaintext: lignone e = 2,718281828 , n - plaintext length Plaintext: lignone
lignone lignoen lignnoe lignneo ligneno ligneon ligonne ligonen ligonne ligonen ligoenn ligoenn lignone lignoen lignnoe lignneo ligneno ligneon ligeonn ligeonn ligenon ligenno ligenno ligenon lingone lingoen lingnoe lingneo lingeno lingeon linogne linogen linonge linoneg linoeng linoegn linnoge linnoeg linngoe linngeo linnego linneog lineong lineogn linenog linengo linegno linegon liongne liongen lionnge lionneg lioneng lionegn liognne liognen liognne liognen liogenn liogenn liongne liongen lionnge lionneg lioneng lionegn lioegnn lioegnn lioengn lioenng lioenng lioengn linnoge linnoeg linngoe linngeo linnego linneog linonge linoneg linogne linogen linoegn linoeng lingone lingoen lingnoe lingneo lingeno lingeon lineogn lineong linegon linegno linengo linenog lienong lienogn liennog lienngo liengno liengon lieonng lieongn lieonng lieongn lieognn lieognn lienong lienogn liennog lienngo liengno liengon liegonn liegonn liegnon liegnno liegnno liegnon lginone lginoen lginnoe lginneo lgineno lgineon lgionne lgionen lgionne lgionen lgioenn lgioenn lginone lginoen lginnoe lginneo lgineno lgineon lgieonn lgieonn lgienon lgienno lgienno lgienon lgnione lgnioen lgninoe lgnineo lgnieno lgnieon lgnoine lgnoien lgnonie lgnonei lgnoeni lgnoein lgnnoie lgnnoei lgnnioe lgnnieo lgnneio lgnneoi lgneoni lgneoin lgnenoi lgnenio lgneino lgneion lgonine lgonien lgonnie lgonnei lgoneni lgonein lgoinne lgoinen lgoinne lgoinen lgoienn lgoienn lgonine lgonien lgonnie lgonnei lgoneni lgonein lgoeinn lgoeinn lgoenin lgoenni lgoenni lgoenin lgnnoie lgnnoei lgnnioe lgnnieo lgnneio lgnneoi lgnonie lgnonei lgnoine lgnoien lgnoein lgnoeni lgnione lgnioen lgninoe lgnineo lgnieno lgnieon lgneoin lgneoni lgneion lgneino lgnenio lgnenoi lgenoni lgenoin lgennoi lgennio lgenino lgenion lgeonni lgeonin lgeonni lgeonin lgeoinn lgeoinn lgenoni lgenoin lgennoi lgennio lgenino lgenion lgeionn lgeionn lgeinon lgeinno lgeinno lgeinon lngione lngioen lnginoe lngineo lngieno lngieon lngoine lngoien lngonie lngonei lngoeni lngoein lngnoie lngnoei lngnioe lngnieo lngneio lngneoi lngeoni lngeoin lngenoi lngenio lngeino lngeion lnigone lnigoen lnignoe lnigneo lnigeno lnigeon lniogne lniogen lnionge lnioneg lnioeng lnioegn lninoge lninoeg lningoe lningeo lninego lnineog lnieong lnieogn lnienog lniengo lniegno lniegon lnoigne lnoigen lnoinge lnoineg lnoieng lnoiegn lnogine lnogien lnognie lnognei lnogeni lnogein lnongie lnongei lnonige lnonieg lnoneig lnonegi lnoegni lnoegin lnoengi lnoenig lnoeing lnoeign lnnioge lnnioeg lnnigoe lnnigeo lnniego lnnieog lnnoige lnnoieg lnnogie lnnogei lnnoegi lnnoeig lnngoie lnngoei lnngioe lnngieo lnngeio lnngeoi lnneogi lnneoig lnnegoi lnnegio lnneigo lnneiog lneiong lneiogn lneinog lneingo lneigno lneigon lneoing lneoign lneonig lneongi lneogni lneogin lnenoig lnenogi lneniog lnenigo lnengio lnengoi lnegoni lnegoin lnegnoi lnegnio lnegino lnegion lognine lognien lognnie lognnei logneni lognein loginne loginen loginne loginen logienn logienn lognine lognien lognnie lognnei logneni lognein logeinn logeinn logenin logenni logenni logenin longine longien longnie longnei longeni longein lonigne lonigen loninge lonineg lonieng loniegn lonnige lonnieg lonngie lonngei lonnegi lonneig loneing loneign lonenig lonengi lonegni lonegin loingne loingen loinnge loinneg loineng loinegn loignne loignen loignne loignen loigenn loigenn loingne loingen loinnge loinneg loineng loinegn loiegnn loiegnn loiengn loienng loienng loiengn lonnige lonnieg lonngie lonngei lonnegi lonneig loninge lonineg lonigne lonigen loniegn lonieng longine longien longnie longnei longeni longein loneign loneing lonegin lonegni lonengi lonenig loening loenign loennig loenngi loengni loengin loeinng loeingn loeinng loeingn loeignn loeignn loening loenign loennig loenngi loengni loengin loeginn loeginn loegnin loegnni loegnni loegnin lngnoie lngnoei lngnioe lngnieo lngneio lngneoi lngonie lngonei lngoine lngoien lngoein lngoeni lngione lngioen lnginoe lngineo lngieno lngieon lngeoin lngeoni lngeion lngeino lngenio lngenoi lnngoie lnngoei lnngioe lnngieo lnngeio lnngeoi lnnogie lnnogei lnnoige lnnoieg lnnoeig lnnoegi lnnioge lnnioeg lnnigoe lnnigeo lnniego lnnieog lnneoig lnneogi lnneiog lnneigo lnnegio lnnegoi lnongie lnongei lnonige lnonieg lnoneig lnonegi lnognie lnognei lnogine lnogien lnogein lnogeni lnoigne lnoigen lnoinge lnoineg lnoieng lnoiegn lnoegin lnoegni lnoeign lnoeing lnoenig lnoengi lninoge lninoeg lningoe lningeo lninego lnineog lnionge lnioneg lniogne lniogen lnioegn lnioeng lnigone lnigoen lnignoe lnigneo lnigeno lnigeon lnieogn lnieong lniegon lniegno lniengo lnienog lnenoig lnenogi lneniog lnenigo lnengio lnengoi lneonig lneongi lneoing lneoign lneogin lneogni lneiong lneiogn lneinog lneingo lneigno lneigon lnegoin lnegoni lnegion lnegino lnegnio lnegnoi legnoni legnoin legnnoi legnnio legnino legnion legonni legonin legonni legonin legoinn legoinn legnoni legnoin legnnoi legnnio legnino legnion legionn legionn leginon leginno leginno leginon lengoni lengoin lengnoi lengnio lengino lengion lenogni lenogin lenongi lenonig lenoing lenoign lennogi lennoig lenngoi lenngio lennigo lenniog leniong leniogn leninog leningo lenigno lenigon leongni leongin leonngi leonnig leoning leonign leognni leognin leognni leognin leoginn leoginn leongni leongin leonngi leonnig leoning leonign leoignn leoignn leoingn leoinng leoinng leoingn lennogi lennoig lenngoi lenngio lennigo lenniog lenongi lenonig lenogni lenogin lenoign lenoing lengoni lengoin lengnoi lengnio lengino lengion leniogn leniong lenigon lenigno leningo leninog leinong leinogn leinnog leinngo leingno leingon leionng leiongn leionng leiongn leiognn leiognn leinong leinogn leinnog leinngo leingno leingon leigonn leigonn leignon leignno leignno leignon ilgnone ilgnoen ilgnnoe ilgnneo ilgneno ilgneon ilgonne ilgonen ilgonne ilgonen ilgoenn ilgoenn ilgnone ilgnoen ilgnnoe ilgnneo ilgneno ilgneon ilgeonn ilgeonn ilgenon ilgenno ilgenno ilgenon ilngone ilngoen ilngnoe ilngneo ilngeno ilngeon ilnogne ilnogen ilnonge ilnoneg ilnoeng ilnoegn ilnnoge ilnnoeg ilnngoe ilnngeo ilnnego ilnneog ilneong ilneogn ilnenog ilnengo ilnegno ilnegon ilongne ilongen ilonnge ilonneg iloneng ilonegn ilognne ilognen ilognne ilognen ilogenn ilogenn ilongne ilongen ilonnge ilonneg iloneng ilonegn iloegnn iloegnn iloengn iloenng iloenng iloengn ilnnoge ilnnoeg ilnngoe ilnngeo ilnnego ilnneog ilnonge ilnoneg ilnogne ilnogen ilnoegn ilnoeng ilngone ilngoen ilngnoe ilngneo ilngeno ilngeon ilneogn ilneong ilnegon ilnegno ilnengo ilnenog ilenong ilenogn ilennog ilenngo ilengno ilengon ileonng ileongn ileonng ileongn ileognn ileognn ilenong ilenogn ilennog ilenngo ilengno ilengon ilegonn ilegonn ilegnon ilegnno ilegnno ilegnon iglnone iglnoen iglnnoe iglnneo iglneno iglneon iglonne iglonen iglonne iglonen igloenn igloenn iglnone iglnoen iglnnoe iglnneo iglneno iglneon igleonn igleonn iglenon iglenno iglenno iglenon ignlone ignloen ignlnoe ignlneo ignleno ignleon ignolne ignolen ignonle ignonel ignoenl ignoeln ignnole ignnoel ignnloe ignnleo ignnelo ignneol igneonl igneoln ignenol ignenlo ignelno ignelon igonlne igonlen igonnle igonnel igonenl igoneln igolnne igolnen igolnne igolnen igolenn igolenn igonlne igonlen igonnle igonnel igonenl igoneln igoelnn igoelnn igoenln igoennl igoennl igoenln ignnole ignnoel ignnloe ignnleo ignnelo ignneol ignonle ignonel ignolne ignolen ignoeln ignoenl ignlone ignloen ignlnoe ignlneo ignleno ignleon igneoln igneonl ignelon ignelno ignenlo ignenol igenonl igenoln igennol igennlo igenlno igenlon igeonnl igeonln igeonnl igeonln igeolnn igeolnn igenonl igenoln igennol igennlo igenlno igenlon igelonn igelonn igelnon igelnno igelnno igelnon inglone ingloen inglnoe inglneo ingleno ingleon ingolne ingolen ingonle ingonel ingoenl ingoeln ingnole ingnoel ingnloe ingnleo ingnelo ingneol ingeonl ingeoln ingenol ingenlo ingelno ingelon inlgone inlgoen inlgnoe inlgneo inlgeno inlgeon inlogne inlogen inlonge inloneg inloeng inloegn inlnoge inlnoeg inlngoe inlngeo inlnego inlneog inleong inleogn inlenog inlengo inlegno inlegon inolgne inolgen inolnge inolneg inoleng inolegn inoglne inoglen inognle inognel inogenl inogeln inongle inongel inonlge inonleg inonelg inonegl inoegnl inoegln inoengl inoenlg inoelng inoelgn innloge innloeg innlgoe innlgeo innlego innleog innolge innoleg innogle innogel innoegl innoelg inngole inngoel inngloe inngleo inngelo inngeol inneogl inneolg innegol inneglo innelgo innelog inelong inelogn inelnog inelngo inelgno inelgon ineolng ineolgn ineonlg ineongl ineognl ineogln inenolg inenogl inenlog inenlgo inenglo inengol inegonl inegoln inegnol inegnlo ineglno ineglon iognlne iognlen iognnle iognnel iognenl iogneln ioglnne ioglnen ioglnne ioglnen ioglenn ioglenn iognlne iognlen iognnle iognnel iognenl iogneln iogelnn iogelnn iogenln iogennl iogennl iogenln ionglne ionglen iongnle iongnel iongenl iongeln ionlgne ionlgen ionlnge ionlneg ionleng ionlegn ionnlge ionnleg ionngle ionngel ionnegl ionnelg ionelng ionelgn ionenlg ionengl ionegnl ionegln iolngne iolngen iolnnge iolnneg iolneng iolnegn iolgnne iolgnen iolgnne iolgnen iolgenn iolgenn iolngne iolngen iolnnge iolnneg iolneng iolnegn iolegnn iolegnn iolengn iolenng iolenng iolengn ionnlge ionnleg ionngle ionngel ionnegl ionnelg ionlnge ionlneg ionlgne ionlgen ionlegn ionleng ionglne ionglen iongnle iongnel iongenl iongeln ionelgn ionelng ionegln ionegnl ionengl ionenlg ioenlng ioenlgn ioennlg ioenngl ioengnl ioengln ioelnng ioelngn ioelnng ioelngn ioelgnn ioelgnn ioenlng ioenlgn ioennlg ioenngl ioengnl ioengln ioeglnn ioeglnn ioegnln ioegnnl ioegnnl ioegnln ingnole ingnoel ingnloe ingnleo ingnelo ingneol ingonle ingonel ingolne ingolen ingoeln ingoenl inglone ingloen inglnoe inglneo ingleno ingleon ingeoln ingeonl ingelon ingelno ingenlo ingenol inngole inngoel inngloe inngleo inngelo inngeol innogle innogel innolge innoleg innoelg innoegl innloge innloeg innlgoe innlgeo innlego innleog inneolg inneogl innelog innelgo inneglo innegol inongle inongel inonlge inonleg inonelg inonegl inognle inognel inoglne inoglen inogeln inogenl inolgne inolgen inolnge inolneg inoleng inolegn inoegln inoegnl inoelgn inoelng inoenlg inoengl inlnoge inlnoeg inlngoe inlngeo inlnego inlneog inlonge inloneg inlogne inlogen inloegn inloeng inlgone inlgoen inlgnoe inlgneo inlgeno inlgeon inleogn inleong inlegon inlegno inlengo inlenog inenolg inenogl inenlog inenlgo inenglo inengol ineonlg ineongl ineolng ineolgn ineogln ineognl inelong inelogn inelnog inelngo inelgno inelgon inegoln inegonl ineglon ineglno inegnlo inegnol iegnonl iegnoln iegnnol iegnnlo iegnlno iegnlon iegonnl iegonln iegonnl iegonln iegolnn iegolnn iegnonl iegnoln iegnnol iegnnlo iegnlno iegnlon ieglonn ieglonn ieglnon ieglnno ieglnno ieglnon iengonl iengoln iengnol iengnlo ienglno ienglon ienognl ienogln ienongl ienonlg ienolng ienolgn iennogl iennolg ienngol iennglo iennlgo iennlog ienlong ienlogn ienlnog ienlngo ienlgno ienlgon ieongnl ieongln ieonngl ieonnlg ieonlng ieonlgn ieognnl ieognln ieognnl ieognln ieoglnn ieoglnn ieongnl ieongln ieonngl ieonnlg ieonlng ieonlgn ieolgnn ieolgnn ieolngn ieolnng ieolnng ieolngn iennogl iennolg ienngol iennglo iennlgo iennlog ienongl ienonlg ienognl ienogln ienolgn ienolng iengonl iengoln iengnol iengnlo ienglno ienglon ienlogn ienlong ienlgon ienlgno ienlngo ienlnog ielnong ielnogn ielnnog ielnngo ielngno ielngon ielonng ielongn ielonng ielongn ielognn ielognn ielnong ielnogn ielnnog ielnngo ielngno ielngon ielgonn ielgonn ielgnon ielgnno ielgnno ielgnon gilnone gilnoen gilnnoe gilnneo gilneno gilneon gilonne gilonen gilonne gilonen giloenn giloenn gilnone gilnoen gilnnoe gilnneo gilneno gilneon gileonn gileonn gilenon gilenno gilenno gilenon ginlone ginloen ginlnoe ginlneo ginleno ginleon ginolne ginolen ginonle ginonel ginoenl ginoeln ginnole ginnoel ginnloe ginnleo ginnelo ginneol gineonl gineoln ginenol ginenlo ginelno ginelon gionlne gionlen gionnle gionnel gionenl gioneln giolnne giolnen giolnne giolnen giolenn giolenn gionlne gionlen gionnle gionnel gionenl gioneln gioelnn gioelnn gioenln gioennl gioennl gioenln ginnole ginnoel ginnloe ginnleo ginnelo ginneol ginonle ginonel ginolne ginolen ginoeln ginoenl ginlone ginloen ginlnoe ginlneo ginleno ginleon gineoln gineonl ginelon ginelno ginenlo ginenol gienonl gienoln giennol giennlo gienlno gienlon gieonnl gieonln gieonnl gieonln gieolnn gieolnn gienonl gienoln giennol giennlo gienlno gienlon gielonn gielonn gielnon gielnno gielnno gielnon glinone glinoen glinnoe glinneo glineno glineon glionne glionen glionne glionen glioenn glioenn glinone glinoen glinnoe glinneo glineno glineon glieonn glieonn glienon glienno glienno glienon glnione glnioen glninoe glnineo glnieno glnieon glnoine glnoien glnonie glnonei glnoeni glnoein glnnoie glnnoei glnnioe glnnieo glnneio glnneoi glneoni glneoin glnenoi glnenio glneino glneion glonine glonien glonnie glonnei gloneni glonein gloinne gloinen gloinne gloinen gloienn gloienn glonine glonien glonnie glonnei gloneni glonein gloeinn gloeinn gloenin gloenni gloenni gloenin glnnoie glnnoei glnnioe glnnieo glnneio glnneoi glnonie glnonei glnoine glnoien glnoein glnoeni glnione glnioen glninoe glnineo glnieno glnieon glneoin glneoni glneion glneino glnenio glnenoi glenoni glenoin glennoi glennio glenino glenion gleonni gleonin gleonni gleonin gleoinn gleoinn glenoni glenoin glennoi glennio glenino glenion gleionn gleionn gleinon gleinno gleinno gleinon gnlione gnlioen gnlinoe gnlineo gnlieno gnlieon gnloine gnloien gnlonie gnlonei gnloeni gnloein gnlnoie gnlnoei gnlnioe gnlnieo gnlneio gnlneoi gnleoni gnleoin gnlenoi gnlenio gnleino gnleion gnilone gniloen gnilnoe gnilneo gnileno gnileon gniolne gniolen gnionle gnionel gnioenl gnioeln gninole gninoel gninloe gninleo gninelo gnineol gnieonl gnieoln gnienol gnienlo gnielno gnielon gnoilne gnoilen gnoinle gnoinel gnoienl gnoieln gnoline gnolien gnolnie gnolnei gnoleni gnolein gnonlie gnonlei gnonile gnoniel gnoneil gnoneli gnoelni gnoelin gnoenli gnoenil gnoeinl gnoeiln gnniole gnnioel gnniloe gnnileo gnnielo gnnieol gnnoile gnnoiel gnnolie gnnolei gnnoeli gnnoeil gnnloie gnnloei gnnlioe gnnlieo gnnleio gnnleoi gnneoli gnneoil gnneloi gnnelio gnneilo gnneiol gneionl gneioln gneinol gneinlo gneilno gneilon gneoinl gneoiln gneonil gneonli gneolni gneolin gnenoil gnenoli gneniol gnenilo gnenlio gnenloi gneloni gneloin gnelnoi gnelnio gnelino gnelion golnine golnien golnnie golnnei golneni golnein golinne golinen golinne golinen golienn golienn golnine golnien golnnie golnnei golneni golnein goleinn goleinn golenin golenni golenni golenin gonline gonlien gonlnie gonlnei gonleni gonlein gonilne gonilen goninle goninel gonienl gonieln gonnile gonniel gonnlie gonnlei gonneli gonneil goneinl goneiln gonenil gonenli gonelni gonelin goinlne goinlen goinnle goinnel goinenl goineln goilnne goilnen goilnne goilnen goilenn goilenn goinlne goinlen goinnle goinnel goinenl goineln goielnn goielnn goienln goiennl goiennl goienln gonnile gonniel gonnlie gonnlei gonneli gonneil goninle goninel gonilne gonilen gonieln gonienl gonline gonlien gonlnie gonlnei gonleni gonlein goneiln goneinl gonelin gonelni gonenli gonenil goeninl goeniln goennil goennli goenlni goenlin goeinnl goeinln goeinnl goeinln goeilnn goeilnn goeninl goeniln goennil goennli goenlni goenlin goelinn goelinn goelnin goelnni goelnni goelnin gnlnoie gnlnoei gnlnioe gnlnieo gnlneio gnlneoi gnlonie gnlonei gnloine gnloien gnloein gnloeni gnlione gnlioen gnlinoe gnlineo gnlieno gnlieon gnleoin gnleoni gnleion gnleino gnlenio gnlenoi gnnloie gnnloei gnnlioe gnnlieo gnnleio gnnleoi gnnolie gnnolei gnnoile gnnoiel gnnoeil gnnoeli gnniole gnnioel gnniloe gnnileo gnnielo gnnieol gnneoil gnneoli gnneiol gnneilo gnnelio gnneloi gnonlie gnonlei gnonile gnoniel gnoneil gnoneli gnolnie gnolnei gnoline gnolien gnolein gnoleni gnoilne gnoilen gnoinle gnoinel gnoienl gnoieln gnoelin gnoelni gnoeiln gnoeinl gnoenil gnoenli gninole gninoel gninloe gninleo gninelo gnineol gnionle gnionel gniolne gniolen gnioeln gnioenl gnilone gniloen gnilnoe gnilneo gnileno gnileon gnieoln gnieonl gnielon gnielno gnienlo gnienol gnenoil gnenoli gneniol gnenilo gnenlio gnenloi gneonil gneonli gneoinl gneoiln gneolin gneolni gneionl gneioln gneinol gneinlo gneilno gneilon gneloin gneloni gnelion gnelino gnelnio gnelnoi gelnoni gelnoin gelnnoi gelnnio gelnino gelnion gelonni gelonin gelonni gelonin geloinn geloinn gelnoni gelnoin gelnnoi gelnnio gelnino gelnion gelionn gelionn gelinon gelinno gelinno gelinon genloni genloin genlnoi genlnio genlino genlion genolni genolin genonli genonil genoinl genoiln gennoli gennoil gennloi gennlio gennilo genniol genionl genioln geninol geninlo genilno genilon geonlni geonlin geonnli geonnil geoninl geoniln geolnni geolnin geolnni geolnin geolinn geolinn geonlni geonlin geonnli geonnil geoninl geoniln geoilnn geoilnn geoinln geoinnl geoinnl geoinln gennoli gennoil gennloi gennlio gennilo genniol genonli genonil genolni genolin genoiln genoinl genloni genloin genlnoi genlnio genlino genlion genioln genionl genilon genilno geninlo geninol geinonl geinoln geinnol geinnlo geinlno geinlon geionnl geionln geionnl geionln geiolnn geiolnn geinonl geinoln geinnol geinnlo geinlno geinlon geilonn geilonn geilnon geilnno geilnno geilnon niglone nigloen niglnoe niglneo nigleno nigleon nigolne nigolen nigonle nigonel nigoenl nigoeln nignole nignoel nignloe nignleo nignelo nigneol nigeonl nigeoln nigenol nigenlo nigelno nigelon nilgone nilgoen nilgnoe nilgneo nilgeno nilgeon nilogne nilogen nilonge niloneg niloeng niloegn nilnoge nilnoeg nilngoe nilngeo nilnego nilneog nileong nileogn nilenog nilengo nilegno nilegon niolgne niolgen niolnge niolneg nioleng niolegn nioglne nioglen niognle niognel niogenl niogeln niongle niongel nionlge nionleg nionelg nionegl nioegnl nioegln nioengl nioenlg nioelng nioelgn ninloge ninloeg ninlgoe ninlgeo ninlego ninleog ninolge ninoleg ninogle ninogel ninoegl ninoelg ningole ningoel ningloe ningleo ningelo ningeol nineogl nineolg ninegol nineglo ninelgo ninelog nielong nielogn nielnog nielngo nielgno nielgon nieolng nieolgn nieonlg nieongl nieognl nieogln nienolg nienogl nienlog nienlgo nienglo niengol niegonl niegoln niegnol niegnlo nieglno nieglon ngilone ngiloen ngilnoe ngilneo ngileno ngileon ngiolne ngiolen ngionle ngionel ngioenl ngioeln nginole nginoel nginloe nginleo nginelo ngineol ngieonl ngieoln ngienol ngienlo ngielno ngielon nglione nglioen nglinoe nglineo nglieno nglieon ngloine ngloien nglonie nglonei ngloeni ngloein nglnoie nglnoei nglnioe nglnieo nglneio nglneoi ngleoni ngleoin nglenoi nglenio ngleino ngleion ngoline ngolien ngolnie ngolnei ngoleni ngolein ngoilne ngoilen ngoinle ngoinel ngoienl ngoieln ngonile ngoniel ngonlie ngonlei ngoneli ngoneil ngoeinl ngoeiln ngoenil ngoenli ngoelni ngoelin ngnloie ngnloei ngnlioe ngnlieo ngnleio ngnleoi ngnolie ngnolei ngnoile ngnoiel ngnoeil ngnoeli ngniole ngnioel ngniloe ngnileo ngnielo ngnieol ngneoil ngneoli ngneiol ngneilo ngnelio ngneloi ngeloni ngeloin ngelnoi ngelnio ngelino ngelion ngeolni ngeolin ngeonli ngeonil ngeoinl ngeoiln ngenoli ngenoil ngenloi ngenlio ngenilo ngeniol ngeionl ngeioln ngeinol ngeinlo ngeilno ngeilon nlgione nlgioen nlginoe nlgineo nlgieno nlgieon nlgoine nlgoien nlgonie nlgonei nlgoeni nlgoein nlgnoie nlgnoei nlgnioe nlgnieo nlgneio nlgneoi nlgeoni nlgeoin nlgenoi nlgenio nlgeino nlgeion nligone nligoen nlignoe nligneo nligeno nligeon nliogne nliogen nlionge nlioneg nlioeng nlioegn nlinoge nlinoeg nlingoe nlingeo nlinego nlineog nlieong nlieogn nlienog nliengo nliegno nliegon nloigne nloigen nloinge nloineg nloieng nloiegn nlogine nlogien nlognie nlognei nlogeni nlogein nlongie nlongei nlonige nlonieg nloneig nlonegi nloegni nloegin nloengi nloenig nloeing nloeign nlnioge nlnioeg nlnigoe nlnigeo nlniego nlnieog nlnoige nlnoieg nlnogie nlnogei nlnoegi nlnoeig nlngoie nlngoei nlngioe nlngieo nlngeio nlngeoi nlneogi nlneoig nlnegoi nlnegio nlneigo nlneiog nleiong nleiogn nleinog nleingo nleigno nleigon nleoing nleoign nleonig nleongi nleogni nleogin nlenoig nlenogi nleniog nlenigo nlengio nlengoi nlegoni nlegoin nlegnoi nlegnio nlegino nlegion nogline noglien noglnie noglnei nogleni noglein nogilne nogilen noginle noginel nogienl nogieln nognile nogniel nognlie nognlei nogneli nogneil nogeinl nogeiln nogenil nogenli nogelni nogelin nolgine nolgien nolgnie nolgnei nolgeni nolgein noligne noligen nolinge nolineg nolieng noliegn nolnige nolnieg nolngie nolngei nolnegi nolneig noleing noleign nolenig nolengi nolegni nolegin noilgne noilgen noilnge noilneg noileng noilegn noiglne noiglen noignle noignel noigenl noigeln noingle noingel noinlge noinleg noinelg noinegl noiegnl noiegln noiengl noienlg noielng noielgn nonlige nonlieg nonlgie nonlgei nonlegi nonleig nonilge nonileg nonigle nonigel noniegl nonielg nongile nongiel nonglie nonglei nongeli nongeil noneigl noneilg nonegil nonegli nonelgi nonelig noeling noelign noelnig noelngi noelgni noelgin noeilng noeilgn noeinlg noeingl noeignl noeigln noenilg noenigl noenlig noenlgi noengli noengil noeginl noegiln noegnil noegnli noeglni noeglin nngloie nngloei nnglioe nnglieo nngleio nngleoi nngolie nngolei nngoile nngoiel nngoeil nngoeli nngiole nngioel nngiloe nngileo nngielo nngieol nngeoil nngeoli nngeiol nngeilo nngelio nngeloi nnlgoie nnlgoei nnlgioe nnlgieo nnlgeio nnlgeoi nnlogie nnlogei nnloige nnloieg nnloeig nnloegi nnlioge nnlioeg nnligoe nnligeo nnliego nnlieog nnleoig nnleogi nnleiog nnleigo nnlegio nnlegoi nnolgie nnolgei nnolige nnolieg nnoleig nnolegi nnoglie nnoglei nnogile nnogiel nnogeil nnogeli nnoigle nnoigel nnoilge nnoileg nnoielg nnoiegl nnoegil nnoegli nnoeigl nnoeilg nnoelig nnoelgi nniloge nniloeg nnilgoe nnilgeo nnilego nnileog nniolge nnioleg nniogle nniogel nnioegl nnioelg nnigole nnigoel nnigloe nnigleo nnigelo nnigeol nnieogl nnieolg nniegol nnieglo nnielgo nnielog nneloig nnelogi nneliog nneligo nnelgio nnelgoi nneolig nneolgi nneoilg nneoigl nneogil nneogli nneiolg nneiogl nneilog nneilgo nneiglo nneigol nnegoil nnegoli nnegiol nnegilo nneglio nnegloi negloni negloin neglnoi neglnio neglino neglion negolni negolin negonli negonil negoinl negoiln negnoli negnoil negnloi negnlio negnilo negniol negionl negioln neginol neginlo negilno negilon nelgoni nelgoin nelgnoi nelgnio nelgino nelgion nelogni nelogin nelongi nelonig neloing neloign nelnogi nelnoig nelngoi nelngio nelnigo nelniog neliong neliogn nelinog nelingo neligno neligon neolgni neolgin neolngi neolnig neoling neolign neoglni neoglin neognli neognil neoginl neogiln neongli neongil neonlgi neonlig neonilg neonigl neoignl neoigln neoingl neoinlg neoilng neoilgn nenlogi nenloig nenlgoi nenlgio nenligo nenliog nenolgi nenolig nenogli nenogil nenoigl nenoilg nengoli nengoil nengloi nenglio nengilo nengiol neniogl neniolg nenigol neniglo nenilgo nenilog neilong neilogn neilnog neilngo neilgno neilgon neiolng neiolgn neionlg neiongl neiognl neiogln neinolg neinogl neinlog neinlgo neinglo neingol neigonl neigoln neignol neignlo neiglno neiglon oignlne oignlen oignnle oignnel oignenl oigneln oiglnne oiglnen oiglnne oiglnen oiglenn oiglenn oignlne oignlen oignnle oignnel oignenl oigneln oigelnn oigelnn oigenln oigennl oigennl oigenln oinglne oinglen oingnle oingnel oingenl oingeln oinlgne oinlgen oinlnge oinlneg oinleng oinlegn oinnlge oinnleg oinngle oinngel oinnegl oinnelg oinelng oinelgn oinenlg oinengl oinegnl oinegln oilngne oilngen oilnnge oilnneg oilneng oilnegn oilgnne oilgnen oilgnne oilgnen oilgenn oilgenn oilngne oilngen oilnnge oilnneg oilneng oilnegn oilegnn oilegnn oilengn oilenng oilenng oilengn oinnlge oinnleg oinngle oinngel oinnegl oinnelg oinlnge oinlneg oinlgne oinlgen oinlegn oinleng oinglne oinglen oingnle oingnel oingenl oingeln oinelgn oinelng oinegln oinegnl oinengl oinenlg oienlng oienlgn oiennlg oienngl oiengnl oiengln oielnng oielngn oielnng oielngn oielgnn oielgnn oienlng oienlgn oiennlg oienngl oiengnl oiengln oieglnn oieglnn oiegnln oiegnnl oiegnnl oiegnln oginlne oginlen oginnle oginnel oginenl ogineln ogilnne ogilnen ogilnne ogilnen ogilenn ogilenn oginlne oginlen oginnle oginnel oginenl ogineln ogielnn ogielnn ogienln ogiennl ogiennl ogienln ognilne ognilen ogninle ogninel ognienl ognieln ognline ognlien ognlnie ognlnei ognleni ognlein ognnlie ognnlei ognnile ognniel ognneil ognneli ognelni ognelin ognenli ognenil ogneinl ogneiln oglnine oglnien oglnnie oglnnei oglneni oglnein oglinne oglinen oglinne oglinen oglienn oglienn oglnine oglnien oglnnie oglnnei oglneni oglnein ogleinn ogleinn oglenin oglenni o
|
|||
|
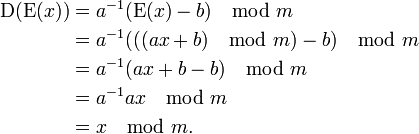
 Caesar cipher, is one of the simplest and most widely known encryption techniques. The transformation can be represented by aligning two alphabets, the cipher alphabet is the plain alphabet rotated left or right by some number of positions.
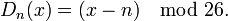
Caesar cipher, is one of the simplest and most widely known encryption techniques. The transformation can be represented by aligning two alphabets, the cipher alphabet is the plain alphabet rotated left or right by some number of positions. 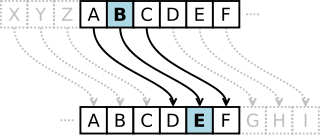 When encrypting, a person looks up each letter of the message in the 'plain' line and writes down the corresponding letter in the 'cipher' line. Deciphering is done in reverse. The encryption can also be represented using modular arithmetic by first transforming the letters into numbers, according to the scheme, A = 0, B = 1,..., Z = 25. Encryption of a letter x by a shift n can be described mathematically as
When encrypting, a person looks up each letter of the message in the 'plain' line and writes down the corresponding letter in the 'cipher' line. Deciphering is done in reverse. The encryption can also be represented using modular arithmetic by first transforming the letters into numbers, according to the scheme, A = 0, B = 1,..., Z = 25. Encryption of a letter x by a shift n can be described mathematically as 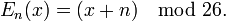 Plaintext: lignone
Plaintext: lignone